Db Fivem.txt ★ Must Try
You will likely see references to these structures within the file: : The most common frameworks for FiveM servers.
: If the credentials are still active, unauthorized users can wipe or dump the live database. db fivem.txt
Since I cannot browse your local files or specific private leaks, this review covers the common contents, security risks, and technical structure found in files with this specific naming convention. 📂 Typical File Contents You will likely see references to these structures
: Exposed IP addresses make the server host a target for network attacks. 🛠️ Technical Breakdown this review covers the common contents
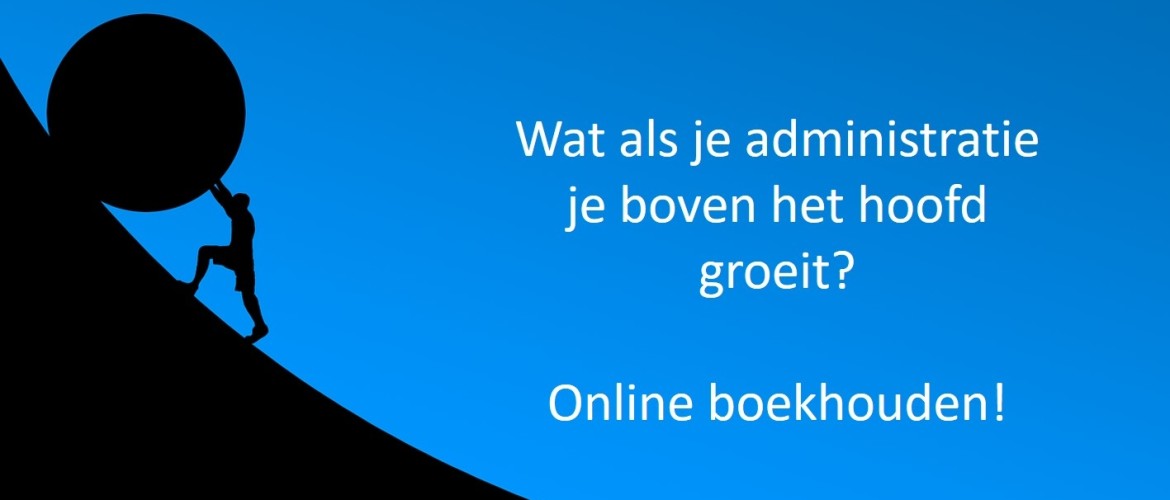
Elma de Bruijn is een visionaire boekhouder en dol op cijfers. Ze inspireert kleine ondernemingen om hun saaie administratie anders te zien. Door skippen van administratie en meer winst maken door betere focus op klanten, dankzij de boekhouding.Waarom? Ze weet uit eigen ervaringen hoe frustrerend hoge accountantskosten voelen en belastingen onnodig vaag zijn. Tevens heeft ze keihard ondergaan hoe belangrijk cijfers zijn, zowel financiële als andere business cijfers.Het maakt of breekt je onderneming, hoe klein dan ook.Ze weet het, omdat ze eens ook ondernemer was zónder kennis. Wees gerust, dat was vóór dat ze accountancy ging studeren;-) Nu weet ze dat het anders kan.