Nemesis - Hub Cracked
It automatically extracts and indexes text from files (using Apache Tika), analyzes DPAPI blobs, and searches for passwords.
In the world of cybersecurity and red teaming, is a powerful data enrichment pipeline and storage system developed by SpecterOps . A "cracked" version of such a hub would imply a bypassed authentication or a leaked version of the proprietary/private infrastructure used by security researchers. Nemesis Hub Cracked
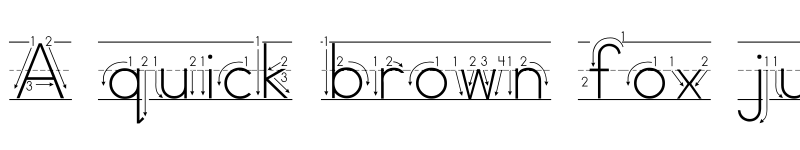
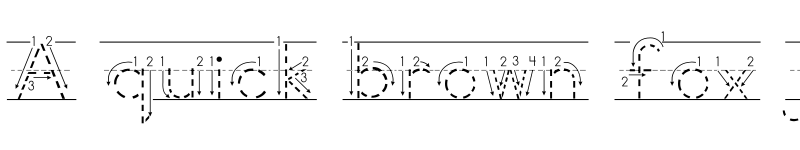
Developers often use libraries like the Orion Library or exploits such as Synapse to build these hubs. 3. Legal and Ethical Dimensions It automatically extracts and indexes text from files
Use the example of the Nemesis System patent (from Warner Bros.), which was a point of contention in the gaming industry regarding how gameplay mechanics are protected. Developers often use libraries like the Orion Library
Using "cracked" software hubs often exposes users to malware, as the tools used to bypass security are frequently bundled with malicious payloads.
For practitioners, a centralized hub like Nemesis allows for semantic search and semantic analysis of massive amounts of looted data during an engagement. 2. Script Hubs and "Cracking" (Gaming Context)
If your paper focuses on the broader implications of "cracking" such hubs: